 “Log Analysis and Security Visualization” is a two-day training class held on March 9th and 10th 2009 in Boston during the SOURCE Boston conference that addresses the data management and analysis challenges of today’s IT environments.
“Log Analysis and Security Visualization” is a two-day training class held on March 9th and 10th 2009 in Boston during the SOURCE Boston conference that addresses the data management and analysis challenges of today’s IT environments.
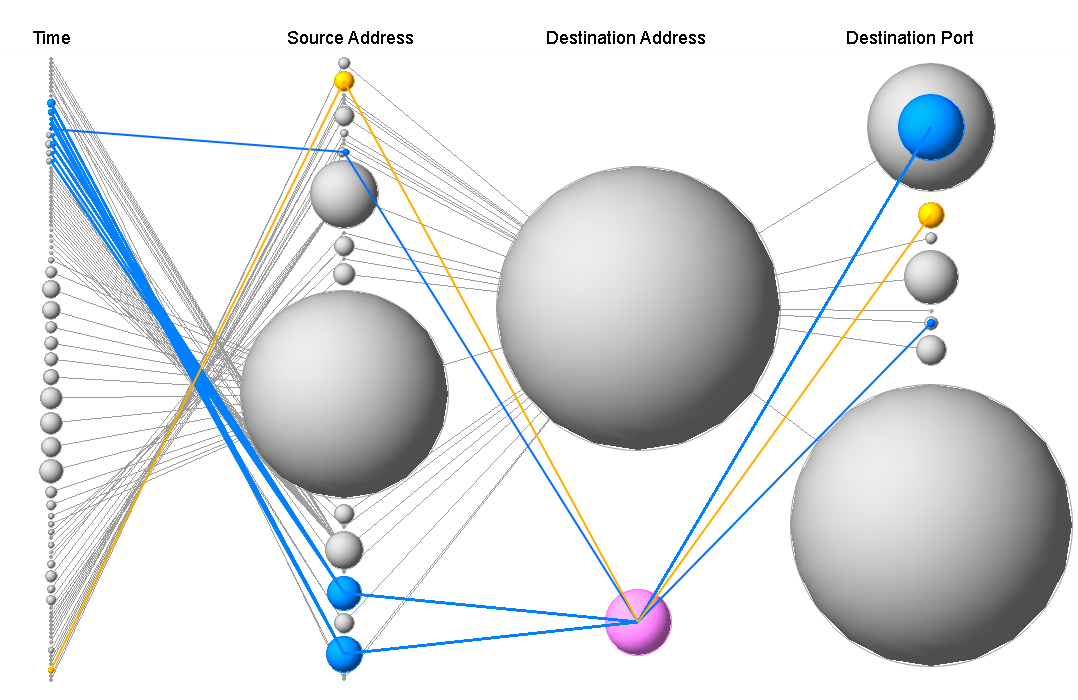
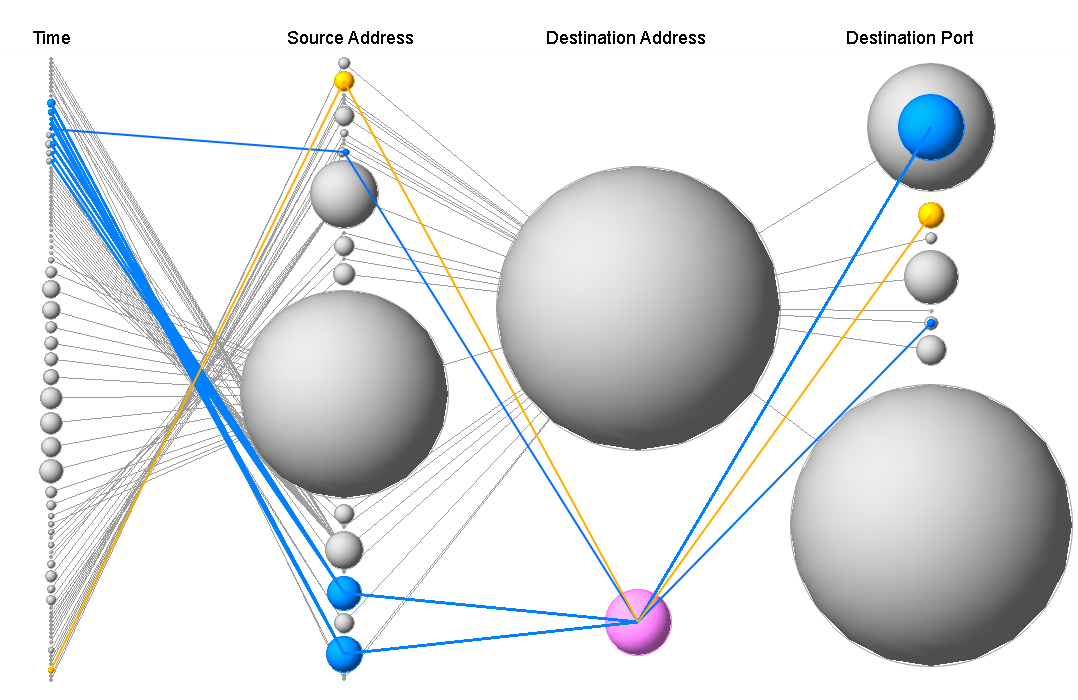
 Students will leave this class with the knowledge to visualize and manage their own IT data. They will learn the basics of log analysis, learn about common data sources, get an overview of visualization techniques, and learn how to generate visual representations of IT data for a number of different use-cases from DoS and worm detection to compliance reporting. The training is filled with hands-on exercises utilizing DAVIX, the open-source data analysis and visualization platform.
Students will leave this class with the knowledge to visualize and manage their own IT data. They will learn the basics of log analysis, learn about common data sources, get an overview of visualization techniques, and learn how to generate visual representations of IT data for a number of different use-cases from DoS and worm detection to compliance reporting. The training is filled with hands-on exercises utilizing DAVIX, the open-source data analysis and visualization platform.
Register today to secure your spot.
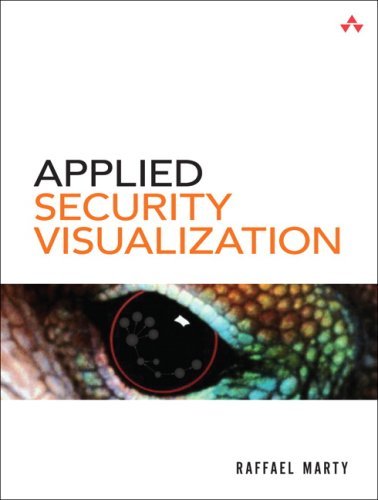
 A little bit more than two years ago, I approached Jessica Goldstein from Addison Wesley to write a book about security visualization. We sat down during BlackHat 2006 and discussed my idea. It didn’t take much to convince her that they should get me on board. I went home after the conference and started putting together a table of contents. Here is the very first TOC that I submitted:
A little bit more than two years ago, I approached Jessica Goldstein from Addison Wesley to write a book about security visualization. We sat down during BlackHat 2006 and discussed my idea. It didn’t take much to convince her that they should get me on board. I went home after the conference and started putting together a table of contents. Here is the very first TOC that I submitted:
- Introduction
- Data Sources
- Visualization
- From Data To Visuals
- Visual Security Analysis
- Situational Awareness
- Perimeter Threat
- Compliance
- Insider Threat
- Data Visualization Tools
If you read the book, you will notice that this is pretty much what I ended up with. More or less. An interesting fact is that at the time of submitting the TOC, I had no idea what to exactly write about in the compliance and insider threat chapters. The even more interesting fact is that a lot of people told me that their favorite chapter is the insider threat chapter.
 After submitting the TOC to Jessica, she had me fill out some more marketing questions about the book. Things like target audience, competitive books, etc. After handing that in, it went silent for a bit. Jessica was selling the book internally. And then things started to look not so good. Jessica went on maternity leave. Kristin took over and got the proposal review process lined up. I asked some people in the industry to have a look over my proposal and provide feedback to the publisher. Questions like: “Why is Raffy the right person to write this book?” “Is there a market for this book?” etc. were being asked. I received the six really great reviews (thanks guys!) mid December 2006. On December 19th, I received an email with the contract to write the book. I sent the contract off to a friend of mine who is a lawyer, just because I was a bit worried about intellectual property rights. After a few emails also with Addison, I felt much better. They are not at all interested in any IP. They just want the copyright, which was totally fine with me. Then, finally, on January 17th, I signed and was under contract to write about 300 pages about security visualization.
After submitting the TOC to Jessica, she had me fill out some more marketing questions about the book. Things like target audience, competitive books, etc. After handing that in, it went silent for a bit. Jessica was selling the book internally. And then things started to look not so good. Jessica went on maternity leave. Kristin took over and got the proposal review process lined up. I asked some people in the industry to have a look over my proposal and provide feedback to the publisher. Questions like: “Why is Raffy the right person to write this book?” “Is there a market for this book?” etc. were being asked. I received the six really great reviews (thanks guys!) mid December 2006. On December 19th, I received an email with the contract to write the book. I sent the contract off to a friend of mine who is a lawyer, just because I was a bit worried about intellectual property rights. After a few emails also with Addison, I felt much better. They are not at all interested in any IP. They just want the copyright, which was totally fine with me. Then, finally, on January 17th, I signed and was under contract to write about 300 pages about security visualization.
After a few days, I received an ISBN number for the book and a ton of material about style guides and how to go about writing the book. All very exciting. I decided to not write my book in TeX, unlike my masters thesis. That was definitely a smart decision. It turned out that using Word wasn’t that bad. The template from Addision made it really easy to format the text correctly. I actually ended up using VI to write the original text without any formatting. Once it was all done, I copied the raw text into Word and started formatting. The reason for doing this is that I am so much quicker in VI than I am in Word. (And hitting the ESC key in Word is not something you want to be doing too much.)
 One of the next steps was to put together a timeline. Well, it was sort of aggressive. The version of the schedule I could find in my archives shows that I was planning on being done mid September 2007. Well, I missed that by only a year 😉 I attribute a lot to the fact that I didn’ really know how to write (seriously) and to the chatpers for which I had to do a lot of research.
One of the next steps was to put together a timeline. Well, it was sort of aggressive. The version of the schedule I could find in my archives shows that I was planning on being done mid September 2007. Well, I missed that by only a year 😉 I attribute a lot to the fact that I didn’ really know how to write (seriously) and to the chatpers for which I had to do a lot of research.
I definitely enjoyed the process of writing the book. The folks at Addison Wesley were awesome. They kept motivating me along the way and provided great insights into the writing process. What I am still very impressed with is the PR aspects. Early on, they hooked me up to film a video cast about the book. After publishing the book, I get about an email a week for some press opportunity. Keep them coming 😉
Here is a fun fact: In ~/Data/projects/vis_addision, where I have all the material for the book, I accumulated 1.1GB of data. Pretty crazy.

 Are you thinking about writing a book? Do it, but make sure you have time! I spent a LOT of time in the local coffee shop (picture on the left). I always had printouts with me to work on corrections. The picture on the right I took at 6.30am in Taipei. Yes, it’s a full-time job! I learned a lot! I made amazing connections. And I had fun! One piece of advice: make sure you have a good publisher!
Are you thinking about writing a book? Do it, but make sure you have time! I spent a LOT of time in the local coffee shop (picture on the left). I always had printouts with me to work on corrections. The picture on the right I took at 6.30am in Taipei. Yes, it’s a full-time job! I learned a lot! I made amazing connections. And I had fun! One piece of advice: make sure you have a good publisher!
I haven’t seen the book in my local Barnes and Nobles yet. Well, I checked two weeks ago. But a friend (@jjx) sent me this picture. So, apparently some book stores have it in stock:

Last week the RSA security conference was held in San Francisco. It’s hard to put all the impressions I gathered during the week into words. Let me just highlight some things that I thought were interesting:

 RSA is a business development conference. It’s been that way for years and this year was definitely not different. At all! Don’t believe me? If even I, who is not in business development can collect this many cards, it has to be a biz dev con.
RSA is a business development conference. It’s been that way for years and this year was definitely not different. At all! Don’t believe me? If even I, who is not in business development can collect this many cards, it has to be a biz dev con.
 The Security Blogger meetup was great. Unfortunately I had to bounce very early. Sorry guys! I would have loved to stick around. The caliber of people hanging out in that room was crazy. Everyone that has a name, and more importantly a voice in the security industry, was there. Thanks to Jennifer for organizing it. Love the t-shirt!
The Security Blogger meetup was great. Unfortunately I had to bounce very early. Sorry guys! I would have loved to stick around. The caliber of people hanging out in that room was crazy. Everyone that has a name, and more importantly a voice in the security industry, was there. Thanks to Jennifer for organizing it. Love the t-shirt!
.
 Talking about everybody being at RSA: I met the CISO of the Vatican 😉
Talking about everybody being at RSA: I met the CISO of the Vatican 😉
.
.
.
.
 We had the first in-person common event expression (CEE) meeting. Some people from XDAS
We had the first in-person common event expression (CEE) meeting. Some people from XDAS
showed up and we had some fairly good discussions around what to do with both the standards, how they can be aligned and how we can move forward.
.
 Walking around on the floor, I found some interesting security visualizations. This one is from DeepSight. Very visually appealing. I haven’t spent much time to understand what’s on the displays, but it looks interesting.
Walking around on the floor, I found some interesting security visualizations. This one is from DeepSight. Very visually appealing. I haven’t spent much time to understand what’s on the displays, but it looks interesting.
.
.

OnSecrity just released another video of the conversation we recorded last year during RSA. I am talking about security visualization in light of the book I am working on. This video cast is the sequel to the first one that I posted a few days ago.
 One of the topics I am discussing in the video is the “false dichotomy” between security and visualization. This is a topic that I talked about during a talk at the MIT Lincoln Labs at the beginning of December. The presentation showed how there are really two disciplines that come together in security visualization: Security and Visualization. The problem with this is that visualization people don’t know much about security and the other way around. It’s a very interesting topic to explore and it explains some of the mistakes that are being made with visualization tools and is also reflected in visualization research.
One of the topics I am discussing in the video is the “false dichotomy” between security and visualization. This is a topic that I talked about during a talk at the MIT Lincoln Labs at the beginning of December. The presentation showed how there are really two disciplines that come together in security visualization: Security and Visualization. The problem with this is that visualization people don’t know much about security and the other way around. It’s a very interesting topic to explore and it explains some of the mistakes that are being made with visualization tools and is also reflected in visualization research.
[tags]visualization, security, videocast[/tags]
 I have been using Linkedin for quite a while now. Today marks the day where I actually have 500 connections. I wonder whether I would be able to go through all of them and remember who each and everyone is. I would probably get a 95% hit rate. I don’t think I am actually making complete use of my network on Linkedin network, but one of my New Year’s resolutions is to get a bit better with my networking.
I have been using Linkedin for quite a while now. Today marks the day where I actually have 500 connections. I wonder whether I would be able to go through all of them and remember who each and everyone is. I would probably get a 95% hit rate. I don’t think I am actually making complete use of my network on Linkedin network, but one of my New Year’s resolutions is to get a bit better with my networking.
Connect to me if I know you and you are not in my network yet!
 I wanted to mention this a long time ago, I am really behind with blogging …
I wanted to mention this a long time ago, I am really behind with blogging …
I started another blog. I hope this is not going to be too confusing.
Here is what goes where:
 There are a number of security conferences out there. Deciding which ones to attend is no easy task. As part of the advisory committee for SOURCE: Boston, I might be a bit biased, but this is going to be a one of a kind security conference. We don’t want to organize yet another security conference. We realize that security has become more and more of a business concern. The security conference of the future needs to bridge the business and the technology. Therefore, three tracks are offered: business, technology, and application security. With the keynote speakers of Dan Geer and Steven Levy, you can be sure to get some interesting perspectives on security!
There are a number of security conferences out there. Deciding which ones to attend is no easy task. As part of the advisory committee for SOURCE: Boston, I might be a bit biased, but this is going to be a one of a kind security conference. We don’t want to organize yet another security conference. We realize that security has become more and more of a business concern. The security conference of the future needs to bridge the business and the technology. Therefore, three tracks are offered: business, technology, and application security. With the keynote speakers of Dan Geer and Steven Levy, you can be sure to get some interesting perspectives on security!
See you March 12th to 14th, 2008 in Boston!
How often is it that you get something in return for reading someone’s blog? Well, today is your lucky day. Are you interested in going to the CSI Conference in Arlington, VA from November 3-9? The first person to send me an email will get a registration code.
Unfortunately, I won’t be able to attend as I am going to be presenting in Jakarta at BCS.
 “Log Analysis and Security Visualization” is a two-day training class held on March 9th and 10th 2009 in Boston during the SOURCE Boston conference that addresses the data management and analysis challenges of today’s IT environments.
“Log Analysis and Security Visualization” is a two-day training class held on March 9th and 10th 2009 in Boston during the SOURCE Boston conference that addresses the data management and analysis challenges of today’s IT environments. Students will leave this class with the knowledge to visualize and manage their own IT data. They will learn the basics of log analysis, learn about common data sources, get an overview of visualization techniques, and learn how to generate visual representations of IT data for a number of different use-cases from DoS and worm detection to compliance reporting. The training is filled with hands-on exercises utilizing DAVIX, the open-source data analysis and visualization platform.
Students will leave this class with the knowledge to visualize and manage their own IT data. They will learn the basics of log analysis, learn about common data sources, get an overview of visualization techniques, and learn how to generate visual representations of IT data for a number of different use-cases from DoS and worm detection to compliance reporting. The training is filled with hands-on exercises utilizing DAVIX, the open-source data analysis and visualization platform.






 RSA is a business development conference. It’s been that way for years and this year was definitely not different. At all! Don’t believe me? If even I, who is not in business development can collect this many cards, it has to be a biz dev con.
RSA is a business development conference. It’s been that way for years and this year was definitely not different. At all! Don’t believe me? If even I, who is not in business development can collect this many cards, it has to be a biz dev con.




 One of the topics I am discussing in the video is the “false dichotomy” between security and visualization. This is a topic that I talked about during a talk at the MIT Lincoln Labs at the beginning of December. The presentation showed how there are really two disciplines that come together in security visualization: Security and Visualization. The problem with this is that visualization people don’t know much about security and the other way around. It’s a very interesting topic to explore and it explains some of the mistakes that are being made with visualization tools and is also reflected in visualization research.
One of the topics I am discussing in the video is the “false dichotomy” between security and visualization. This is a topic that I talked about during a talk at the MIT Lincoln Labs at the beginning of December. The presentation showed how there are really two disciplines that come together in security visualization: Security and Visualization. The problem with this is that visualization people don’t know much about security and the other way around. It’s a very interesting topic to explore and it explains some of the mistakes that are being made with visualization tools and is also reflected in visualization research.